

In a data-driven financial landscape, cybercrime has become a significant concern for regulators and institutions alike, with criminals exploiting computer systems and online financial services to perpetrate money laundering, fraud, and other crimes. The cost of cybercrime money laundering is expected to reach around $10.5 trillion by 2025.
The Covid-19 pandemic exacerbated the threat posed by cybercrime and money laundering methodologies. With increased online financial activity and changes in customer behavior, criminals could target vulnerable individuals and institutions more easily and take advantage of regulatory blind spots.
Given the threats and the potential for significant penalties, banks, financial institutions, and other obligated entities should ensure that they understand the compliance risks they face and be prepared to deploy a suitable cybercrime and money laundering response.
What is cybercrime, and how does it relate to money laundering?
Cybercrime is any illegal activity that involves a computer, the internet, or a networked device. With the emergence and growing ubiquity of online commercial and financial services (especially since the Covid-19 crisis), criminals have had greater opportunities to derive profits from online fraud and theft and, with that, a greater need to conceal the source of their illegal funds.
Computers and computer systems offer money launderers a degree of anonymity and the opportunity to move illegal funds quickly between accounts while avoiding the customer due diligence (CDD) and transaction monitoring checks that conventional anti-money laundering and combatting the financing of terrorism (AML/CFT) systems would normally impose.
Types of cybercrime
Cybercrimes can be separated into two categories:
- Cybercrimes, or cyber events, involve compromising or gaining unlawful access to a computer or computer system along with its services, resources, and information. Cybercriminals may use these approaches to steal financial data, card payment data, and user identities. Common examples include hacking, ransomware, and malware.
- Cyber-enabled crimes are when criminals use computers or computer systems to commit offenses, such as money laundering. Cyber-enabled crime is on the rise and includes intellectual property crimes, phishing, voice phishing, romance scams, fraud, weapons trafficking, drug dealing, business email compromise, and online content crimes, including sharing child abuse imagery.
Cybercrime trends
In November 2022, the Financial Crimes Enforcement Network (FinCEN) published a Financial Trend Analysis report on ransomware trends between July 2021 and December 2021. The analysis found that reported ransomware-related incidents increased by over 50 percent from 2020. Additionally, in the first half of 2022, it is estimated that 236.7 million ransomware attacks occurred, with an average cost of $1.85 million per incident.
Emerging cybercrime typologies and methods that are increasing include:
- Cyber-terrorism.
- Crypto-jacking and attacks via the Internet of Things (IoT), such as smart speakers.
- Cyber-attacks against critical infrastructure, including healthcare (attacks on the health sector were up 60 percent in 2022 compared to 2021).
- Criminals targeting medium and small-sized companies versus larger organizations because they are seen as an easier target.
- Cybercrime money laundering criminals requesting ransom payments in Bitcoin.
- A decrease in the time it takes attackers to perform end-to-end ransomware attacks. In some cases, attackers may have only been inside the company’s system for four days.
Cybercrime and AML
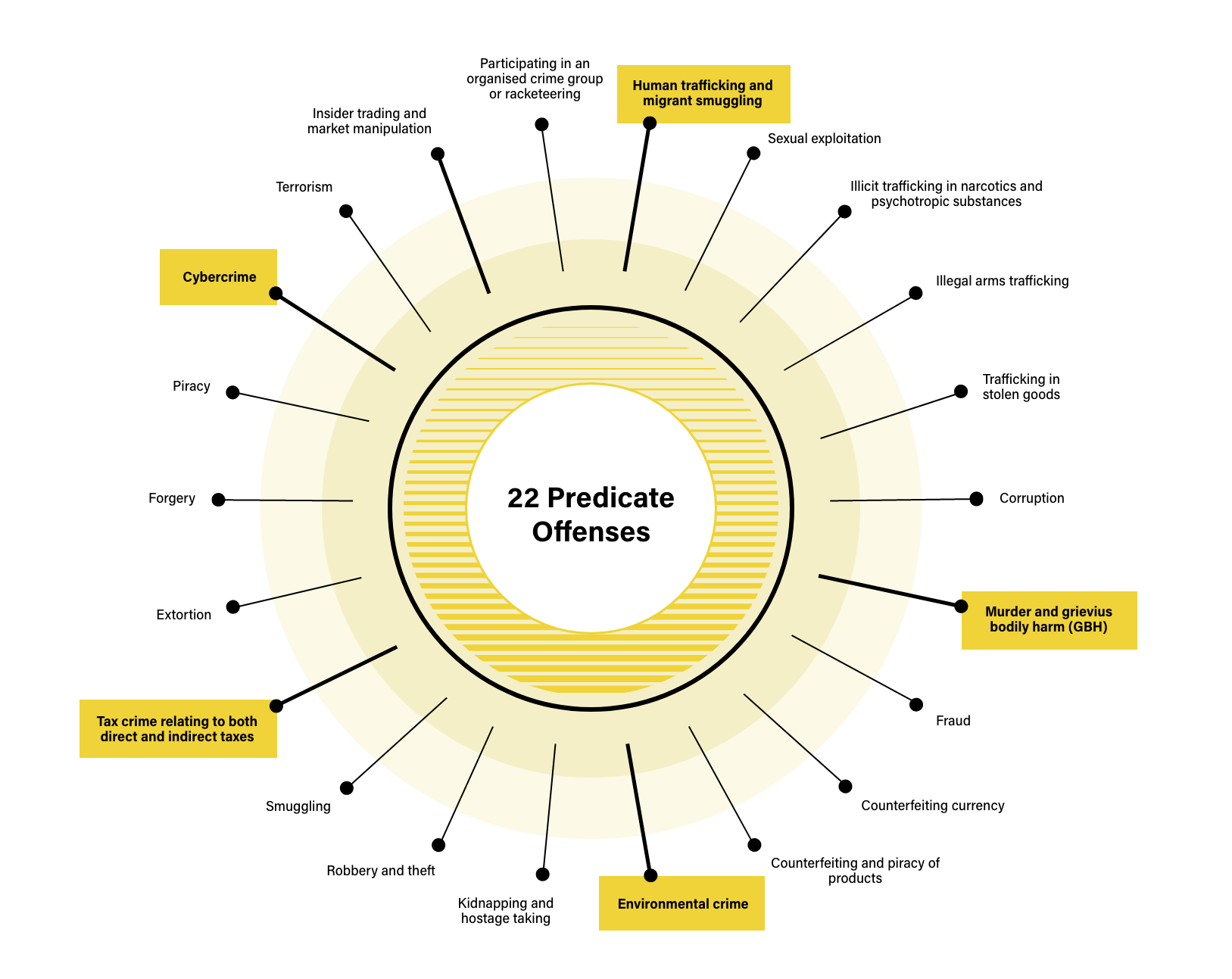
Cybercrime is considered a predicate offense because it generates illegal proceeds that need to be disguised by laundering before they can be entered into the legitimate financial system. The European Union’s 6th Anti-Money Laundering Directive (6AMLD) codifies this by including cybercrime in its list of 22 money laundering predicate offenses, joining existing predicate offenses like human trafficking, drug trafficking, counterfeiting, and theft.
What is cyber laundering?
Cyber laundering is when criminals use the internet to establish anonymity or non-traceability for laundering money.
Types of cyber laundering
Two of the most common types of cyber laundering are:
- Instrumental digital laundering – when one (or more) steps of the crime are carried out using digital methods.
- Integral digital laundering – when the whole crime journey is undertaken digitally.
Methods used in cyber laundering
Some of the most popular methods used in cyber laundering include:
- Using social media to coerce members of the public to deposit funds through the guise of a “donation” or other fundraising activity. After the payments have been made, the fraudsters usually transfer the funds quickly to other mobile services accounts.
- Illegally obtaining someone’s identity credentials via various digital methods, such as phishing through email scams, voice calls, or instant messaging platforms.
- Online gambling platforms and online lottery schemes.
- After hacking into victims’ email accounts, fraudsters often perpetrate wire fraud by sending instructions to the victims’ banks about transferring funds to other accounts, usually in a different jurisdiction.
Cybercrime money laundering red flags
Cybercrimes often exhibit ‘red flag’ characteristics that can aid firms in detecting and preventing money laundering and in enhancing their compliance performance.
Since the COVID-19 pandemic, cybercrime has increased by 600 percent. In response, the Financial Crimes Enforcement Network (FinCEN) released a series of advisories calling financial institutions to be particularly vigilant for COVID-19-related attempts to launder money.
With the FinCEN advisories in mind, red flags that indicate cybercrime money laundering include:
- Unusual transactional behavior such as suddenly increased frequencies or volumes of online transactions.
- Online transactions involving parties located in high-risk countries.
- Recently opened online accounts that receive large deposits or conduct large transactions that are inconsistent with the customer’s profile or account history.
- A high number of payments made with prepaid cards or with virtual currencies such as Bitcoin.
- Correspondence sent to or from customers that indicate phishing attempts, frequent misspellings in the text of correspondence, or suspicious address credentials.
- Email or social media solicitations for fraudulent charity donations.
- Charitable organizations that do not have an in-depth history or cannot be independently verified as legitimate organizations.
How to comply with cybercrime regulations
Under Financial Action Task Force (FATF) recommendations, banks, financial institutions, and other obligated entities must put risk-based AML/CFT programs in place to deal with the AML/CFT threats that they face from cybercrime. In practice, this means that firms must conduct risk assessments of their customers and deploy a proportionate AML response. In the context of cybercrime, this means that firms must work to identify their customers and to monitor their transactional behavior on an ongoing basis with the following AML/CFT measures and controls:
- Customer due diligence (CDD): Since cyber-criminals often exploit the anonymity of online financial services, firms should conduct suitable due diligence to establish and verify customer identities and the nature of the business in which they are engaged.
- Transaction monitoring: Cybercrimes often involve the rapid transfer of illegal funds to different accounts in locations around the world. With that in mind, firms should monitor their customers’ transactions for indications of attempts to launder money.
- Sanctions screening: Firms must screen their customers against relevant international sanctions and watch lists such as the OFAC Sanctions List and the UNSC Consolidated List.
- Politically exposed person (PEP) screening: PEPs are at a higher risk of being involved in cybercrime money laundering. Accordingly, firms must screen their customers to establish their PEP status and adjust their AML response accordingly.
- Adverse media monitoring: Adverse media and negative news stories often indicate that customers are involved in attempts to launder the proceeds of cybercrime. Firms should monitor for adverse media stories that involve their customers on an ongoing basis, including both conventional screen and print media and online sources.
It is vital that compliance staff report cybercrimes by filling in Suspicious Activity Reports (SARs). FINCEN advises any professional detecting a cybercrime to use the key term “CYBERFIN-2021-A004” and select SAR field 42 (cyber event).
Demo Request
See how 1000+ leading companies are screening against the world's only real-time risk database of people and businesses.
Request demoOriginally published 24 February 2021, updated 12 February 2025
Disclaimer: This is for general information only. The information presented does not constitute legal advice. ComplyAdvantage accepts no responsibility for any information contained herein and disclaims and excludes any liability in respect of the contents or for action taken based on this information.
Copyright © 2026 IVXS UK Limited (trading as ComplyAdvantage).
