

Despite being one of the most important lines of defense for financial institutions (FIs), many businesses struggle to balance effective compliance and security with ease of use during payment screening.
This guide delves into what payment screening is, why it can pose significant risk and challenges if not done properly, and how intelligent design and AI-driven technology can help scale your business and leverage speed and agility.
What is payment screening?
Payment screening is the process of analyzing, verifying, and validating incoming and outgoing transactions. Its purpose is to understand the risk of impropriety or criminal activity in any given payment. By screening payments, FIs can quickly decide whether to escalate a potentially illicit transaction or allow a legitimate payment to proceed.
This allows firms to remain compliant with anti-money laundering and counter-terrorist financing regulations (AML/CFT) worldwide while protecting their customers and themselves from criminal attempts to siphon money or abuse payment rails. Because of this, FIs of all sizes must be able to screen all types of digital payments, from standard credit card transactions to faster cross-border payment schemes like FedNow. For domestic transactions or Instant SEPA credit, regulatory requirements generally mandate daily customer-level screening rather than transaction-level payment screening.
The difference between payment screening and transaction monitoring
While sometimes confused, these two processes have complementary roles within a compliance program:
- Payment screening as an interception function: Payment screening detects individual payments before they are processed to stop illicit funds in their tracks and prevent high-risk activity from entering or leaving the financial institution.
- Transaction monitoring as an analytical function: Transaction monitoring scans post-event activities an FI undertakes to observe, record, and respond to customer interactions with its services, allowing teams to find behavioral patterns and anomalies over time.
Each screening process involves similar steps but can vary based on the specific risk factors involved in the transactions being screened.
Why are payment screening regulations tightening?
Payment screening is necessary because FIs worldwide are subject to many regulations and recommendations to tackle criminal activity, such as money laundering, terrorist financing, and fraud. Regulatory bodies such as Financial Action Task Force (FATF), the Financial Crimes Enforcement Network (FinCEN), the Financial Conduct Authority (FCA), and Monetary Authority of Singapore (MAS), are tightening their requirements around payment screening.
Firms that cannot demonstrate real-time, explainable screening may face significant fines, reputational damage, and the loss of correspondent banking relationships. While specific frameworks like the EU’s Payment Services Regulation (PSR) and the Third Payment Services Directive (PSD3), the US’s Electronic Fund Transfer Act EFTA, or the UK’s Payment Services Regulations 2017 (PSRs 2017) vary per the region they address, they require firms to demonstrate a robust, auditable capacity to monitor and screen cross-border and high-risk payments before execution.
What are the most common risks associated with payments?
Some common issues to look out for when processing payments include:
- Identity theft: This is when a criminal steals personal information and banking details to make purchases online, masquerading as an institution’s customer.
- Friendly fraud: This occurs when a customer uses their own card to make a purchase and then disputes the charge with the FI without a legitimate reason.
- Authorized push fraud: This is when criminals coerce or manipulate victims into depositing money into their accounts through unscrupulous means.
- ‘Clean’ fraud: This is when a criminal uses customer credentials to make a purchase but then uses stolen payment information to evade fraud detection protocols. It’s particularly hard to detect, especially with the rise of AI-generated synthetic identities and Deepfake-as-a-Service technologies.
- Money laundering: This is when a customer or criminal makes payments as part of a larger conspiracy to obfuscate the origin or destination of money, in a bid to make it appear legitimate.
- Terrorist financing: This occurs when a payment is made to a specific party to finance terrorist activity while disguised as a more innocuous transaction.
What are the core elements of a payment screening process?
An effective payment screening process involves coordinating several different components. These include:
- A clearly defined risk-based approach (RBA): Firms need to translate their risk tolerance into clear policies and procedures. A no-code screening configuration UIs enables firms to control settings for names, BIC codes, and reference text without needing engineering support. This self-service approach ensures the system precisely matches the firm’s RBA.
- Clean, up-to-date, connected data: To ensure optimal screening decisions are being made at scale, businesses need the data informing those decisions – customer histories, third-party inputs, sanctions data – to be reliable.
- Updated employee training: Whether they’re implementing automation in the screening process or handling exceptions when they arise, employees need to be trained in the most relevant procedures, scenarios, and regulations.
- Intuitive, intelligent technology: Payment screening software needs to update as rapidly as data feeds while still being intuitive enough to ensure compliance teams can manage cases at speed. Alert muting now helps analysts to prevent alerts from confirmed false positives to reappear in future cases, which contributes to reducing alert fatigue.
- Continuous auditing processes: To continue improving the payment screening process, firms need an independent function dedicated to auditing every aspect of it to identify weaknesses and oversee prompt implementation.
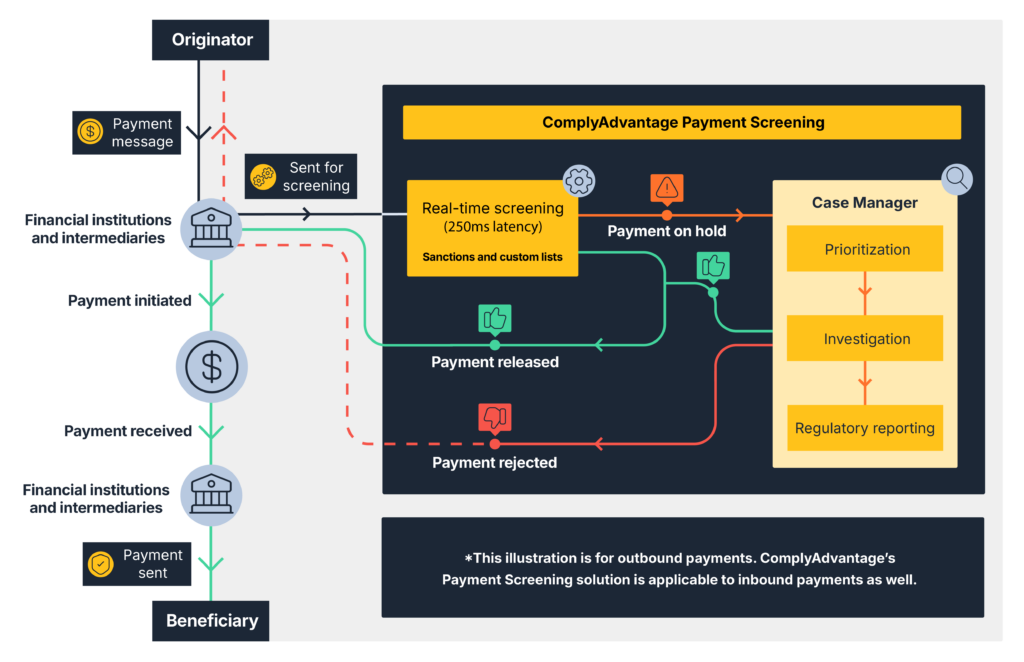
How does the payment screening process work?
Once the initial payment message has been sent or received, the payment screening process begins, which can be broken down into five distinct stages:
Stage 1: Customer authentication and data verification
During the initial stage of a transaction, it is essential to gather all relevant data to support the payment message during validation. This includes the transaction amount, information about the sender and receiver, their respective locations, and any other essential details required for the payment to proceed smoothly.
Stage 2: Risk-based customer due diligence (CDD)
Next, a risk assessment needs to be conducted to determine the probability of criminal activity based on the various degrees of customer due diligence outlined in the firm’s risk-based approach. This involves an evaluation based on the customer’s previous transaction patterns, generalized historical crime patterns, and the jurisdictions in question.
Stage 3: Sanctions, watchlists, and PEP screening
Then, businesses need to scan sanctions lists, watchlists, and politically exposed person (PEP) lists to identify potential matches with the sender, receiver, or related organizations. If the payment is legitimate, these initial checks should take only milliseconds. If it isn’t, the case should be escalated.
Stage 4: Escalation
If preceding stages raise a red flag, businesses will then escalate the payment to a dedicated team specializing in enhanced due diligence (EDD) processes. If this team agrees the payment is suspicious, it may be declined. If reviewed and flagged as a false positive, analysts can prevent future disruptions for the same safe entity.
Stage 5: Reporting
Finally, if a payment, sender, or receiver is flagged as suspicious, the firm is required to immediately provide the relevant documentation to the authorities. Businesses must maintain detailed records of all these stages for auditability and regulator collaboration.
The challenges of payment screening
Payment screening helps FIs overcome some serious risks. However, given the complexity of all the moving pieces involved in these procedures, it brings unique challenges, including:
- Speed: The value proposition for digital financial services is increasingly about convenience, so legitimate payments need to be validated in milliseconds without adding friction to the overall customer experience.
- False positives and analyst fatigue: Inadequate screening errs on the side of caution and stops even mildly suspicious transactions. This overburdens the compliance team with endless false positive alerts and repeat reviews of the same counterparties, hindering operations.
- Staying up to date with sanctions lists: A fast screening process is ultimately no better if it’s unable to keep up with the latest developments in international crime and rapidly changing global watchlists.
- The complexity of the process: Professionals can quickly become tied in knots between disparate data feeds and applications for cases, relationships, and reporting if their tools aren’t vertically integrated.
- Maintaining auditability: At a regulatory level, many firms struggle to provide the kind of transparency, logs, and workflow documentation required by auditors.
The importance of technology in payment screening
Given these challenges, firms must leverage advanced technologies to automate and scale their AML payment screening processes. By automating fundamental steps such as customer authentication and sanctions screening, firms can better balance speed and security.
Even when cases are escalated and need manual review, software can provide compliance teams with an intuitive workflow for rapidly managing anomalies, applying self-service configuration, and ensuring zero data is lost across the audit trail.
Get a competitive advantage by utilizing intelligent payment screening
FIs of all sizes rely on ComplyAdvantage for intelligent, swift payment screening at scale. As the demand for real-time payments grows, legacy screening methods struggle to balance the need for speed with robust security, often leading to friction for legitimate customers or exposure to financial crime.
With ComplyAdvantage Mesh, you can address this challenge directly using a single, AI-native platform to deliver significant operational benefits by:
- Processing payments at high velocity: Payment Screening is built to handle high-volume, real-time payment rails. By leveraging data-optimized screening algorithms and cloud technology, you can process most transactions in <250ms at P90 (supporting 100+ TPS sustained), improving the experience for your legitimate customers without compromising the integrity of compliance checks.
- Scaling your business while reducing false positives: By tackling the overwhelming volume of false alerts via powerful muting capabilities that stop analysts from re-reviewing the same safe profiles, you enable them to focus their time and resources on genuine threats.
- Empowering compliance teams with autonomy: A native, no-code Screening Configuration UI allows your teams to easily adjust fuzziness settings for names, BIC codes, and reference text. This means you can swiftly adapt your risk models to rapidly-changing regulations without relying on engineering support.
- Staying ahead of risk with real-time intelligence: Because screening against outdated information is a risk for any firm, access market-leading data from human-validated sanctions lists, watchlists, and PEP lists, with ongoing system-wide updates so you get the most current data.
A cloud-based compliance platform, ComplyAdvantage Mesh combines industry-leading AML risk intelligence with actionable risk signals to screen customers and monitor their behavior in near real time.Discover integrated, real-time payment screening with Mesh
Originally published 04 March 2024, updated 01 June 2026
Disclaimer: This is for general information only. The information presented does not constitute legal advice. ComplyAdvantage accepts no responsibility for any information contained herein and disclaims and excludes any liability in respect of the contents or for action taken based on this information.
Copyright © 2026 IVXS UK Limited (trading as ComplyAdvantage).
