

For banks and other financial institutions (FIs), an anti-money laundering (AML) compliance program is a critical defense against financial crime and a regulatory requirement. To manage these complex obligations, leading institutions anchor their programs with a comprehensive AML compliance checklist.
This guide provides a definitive 10-point checklist, updated for the technological and regulatory landscape of 2026. It is optimized to help your organization achieve compliance, enhance efficiency, and demonstrate robust governance to auditors and regulators.
The core AML compliance checklist for banks
A forward-looking AML compliance checklist should incorporate the following 10 essential pillars, ensuring a practical, proactive approach to upholding AML best practices.
1. Appoint an independent compliance officer
In line with the Financial Action Task Force (FATF) recommendations, a bank must appoint a compliance officer to oversee its AML compliance program and serve as a liaison to regulators. The compliance officer should be a senior employee with the independence, authority, and resources to oversee the entire AML framework. Their key responsibilities include:
- Developing, implementing, and maintaining the firm’s AML policies and procedures.
- Acting as the primary liaison with regulatory bodies and law enforcement.
- Overseeing risk assessments and independent testing of the AML program.
- Managing the investigation and submission of suspicious activity reports (SARs).
- Advising senior management on emerging threats and necessary compliance regulations. This includes US-specific rules such as the Bank Secrecy Act (BSA), the UK’s Money Laundering Regulations (MLRs), and the EU’s Anti-Money Laundering Directives (AMLDs).
2. Implement a risk-based approach
A one-size-fits-all strategy is no longer viable. The FATF advises banks to adopt a dynamic risk-based approach, tailoring their AML efforts to the specific risks they face.
“A ‘one-size-fits-all’ approach would be inconsistent with the proper implementation of a risk-based approach as stipulated under Recommendation 1 of the FATF Standards.”
Source: FATF Recommendations, updated October 2025
This involves a continuous cycle of assessing, mitigating, and monitoring risks across key areas:
- Products & services: High-risk products, such as international wire transfers or anonymous bearer share accounts, require more stringent scrutiny than standard transactions. Developing a nuanced awareness of each product’s risk profile enables banks to allocate resources judiciously.
- Client profiles: Risk ratings must be assigned based on factors like customer type, occupation, source of funds (SoF), and geographic location. High-net-worth individuals, politically exposed persons (PEPs), or entities operating in high-risk industries demand heightened scrutiny.
- Geography: Operations in or transactions with jurisdictions listed on the FATF’s grey and black lists necessitate enhanced due diligence (EDD). Certain areas may pose higher AML risks due to the prevalence of money laundering (ML) activities, economic instability, or weak regulatory frameworks.
- Transaction patterns: Transaction monitoring systems should detect anomalies relative to a customer’s expected activity. Analyzing transaction patterns helps banks identify anomalies and potential red flags.
3. Develop internal AML policies
Your AML program must be formally documented in a comprehensive, board-approved written policy. This document is the blueprint for your firm’s compliance efforts. For firms operating in the US, this must align with the BSA and AML compliance regulations outlined in the Financial Industry Regulatory Authority’s (FINRA) Rule 3310.
Similarly, firms in the UK should follow the guidance of the Joint Money Laundering Steering Group (JMLSG), while those in Singapore must adhere to the notices issued by the Monetary Authority of Singapore (MAS).
A bank’s internal AML policies should include:
- A checklist to ensure new products are compliant.
- Procedures for customer due diligence (CDD), including reporting suspicious transactions and identity verification.
- Guidelines for record-keeping and information sharing.
- Protocols for conducting EDD on high-risk clients.
- An outline of the transaction monitoring and SAR filing processes.
- The designated roles and responsibilities of AML staff are to maintain proper operations and reporting.
Firms can review FINRA’s free-to-use AML checklist template for small and medium-sized organizations for more information.
4. Establish an AML training program
FATF recommendations emphasize the need for continuous, role-specific training for all relevant employees to remain capable of recognizing suspicious activity. As a result, a bank’s compliance checklist should include an ongoing AML training schedule to enable all employees to adapt to new legislation and emerging criminal methodologies. Essential training modules include:
- Recognizing and escalating potential red flags of financial crime.
- The practical application of the bank’s risk-based approach and understanding of its specific protocols and procedures.
- Specific responsibilities under the know your customer (KYC), CDD, and SAR filing procedures.
- Proper use of the bank’s AML technology and software stack.
- The legal and reputational consequences of compliance failures.
- Any other necessary documentation for the specific role.

Enhance your AML expertise
Access our library of expert-led webinars to sharpen your skills and deepen your industry knowledge.
Learn more5. Perform CDD
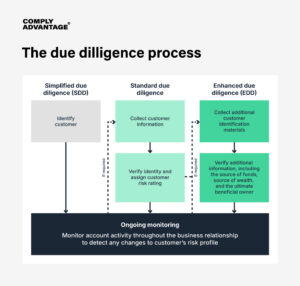
You cannot manage risk without knowing your customer. A robust CDD process, from onboarding through the customer lifecycle, is the cornerstone of AML compliance. A rigorous CDD process should include the following:
- Identification: Collect and verify a customer’s identity (name, DOB, address, official identification number) using reliable, independent data and documents.
- Purpose: Understand and document the intended nature of the business relationship.
- Beneficial ownership: For corporate accounts, identify and verify the ultimate beneficial owners (UBOs), the individuals who ultimately own or control the entity.
For customers identified as higher risk, banks have a responsibility to conduct EDD, which involves a deeper investigation into their source of wealth and the nature of their transactions.
Therefore, banks should ideally include PEP screening in their AML checklist during onboarding and throughout the business relationship to ensure any status changes are detected.
6. Screen all customers against sanctions and watchlists
Banks are prohibited from transacting with individuals, entities, or nations on international sanctions lists. Your AML checklist must include a robust, real-time screening process against all relevant lists, including those issued by national and international authorities. Sanctions screening best practices include:
- Ensuring high-quality customer data is collected from verified sources.
- Using the right technology to automate and speed up sanctions screening.
- Ensure the relevant teams are trained with accurate, firm-specific information.
- Ensure stakeholders know the right actions to take when a red flag arises.
Key lists for screening include:
- National lists: In the US, for example, the US Treasury’s OFAC Specially Designated Nationals (SDN) List. Other key examples include the UK’s Sanctions List, the EU’s Consolidated Financial Sanctions List, and Australia’s Consolidated List.
- Supranational lists: This includes the UN Security Council Consolidated List.
- Lists of PEPs to identify individuals who may pose a higher risk of bribery and corruption.
7. Continuous transaction monitoring
Real-time monitoring of customer transactions is essential for detecting suspicious activity. Your system should continuously flag behavior that deviates from a customer’s established risk profile. Key areas for monitoring include:
- Transactions exceeding regulatory thresholds.
- Unusual patterns, such as a sudden surge in transfers or structuring (making many small deposits to avoid a threshold).
- Transactions involving high-risk jurisdictions.
- Transactions with PEPs or with sanctioned individuals.
- Activity linked to known adverse media reports about a customer.
8. Report suspicious activities
When transaction monitoring or other activities identify a reasonable suspicion of ML, terror financing (TF), or other illicit activities, the institution must file a SAR with its jurisdiction’s Financial Intelligence Unit (FIU). Examples of FIUs include Financial Crimes Enforcement Network (FinCEN) in the US, the National Crime Agency (NCA) in the UK, or AUSTRAC in Australia. It’s essential that the process for submitting a SAR is robust, and must be:
- Confidential: The customer must not be “tipped off” that a report is filed.
- Prompt: Reports must be filed within the statutory deadlines.
- Detailed: The report should clearly document the entity involved, the transactions that occurred, when and where they occurred, and why they are considered suspicious.
9. Maintain clear AML records
Regulators require banks to “show their work.” Meticulous record-keeping is non-negotiable and essential for demonstrating compliance during an audit.
Banks are required to maintain the following AML records:
- All customer identification and verification data.
- CDD and EDD documentation and risk-scoring methodologies, including PEP and adverse media documentation.
- Records of all transactions.
- Copies of all SARs filed.
- Documentation of AML training programs and attendee lists.
- Records of internal audits, correspondence between the engagement and onboarding teams, and any corrective actions taken.
While there is no standard set of record-keeping requirements applicable to all businesses, there should be clear documentation to support a firm’s onboarding procedures, demonstrating why a particular client is onboarded and the steps they went through.
The duration for which businesses should retain this information depends on the laws and regulations in their jurisdiction. For instance, under the BSA, firms are generally required to retain records for 5 years, whereas Australia’s Anti-Money Laundering and Counter-Terrorism Financing Act 2006 (AML/CTF Act) mandates a 7-year retention period.
Firms must also maintain records of any changes to their formal risk-based assessment, AML/CFT, and sanctions compliance policies. policies.
10. Leverage advanced AML technology and AI
Manual processes and incumbent standard AI systems, which are rule-based engines that generate simple alerts, are no longer sufficient to manage the scale and complexity of modern financial crime.
Advanced, agentic technology is required to keep pace with sophisticated financial criminals, delivering the deep, contextual intelligence and end-to-end automation needed to uncover hidden risks.
Our global survey of 600 compliance decision-makers found that while 100% of firms expect benefits from predictive and agentic AI, there is an execution gap, with only 33% confirming they are currently using agentic AI for customer screening, and 32% for transaction monitoring. This gap presents a critical opportunity for forward-thinking banks to gain a significant competitive advantage.
Glossary
Agentic AI describes AI models that are equipped with agency: the ability to plan, reason, and execute tasks in pursuit of objectives. Unlike ‘standard AI’ systems that are limited to a single output (e.g. a model that flags a transaction as suspicious based on a pre-set rule), agentic AI can interact with external tools, adapt behavior based on context, and operate iteratively until the desired outcome is achieved. An example of agentic AI is the auto-remediation of level 1 alerts – where the AI not only identifies a low-risk alert but also independently gathers the necessary data, drafts the closure narrative, and closes the case without human intervention.
Predictive AI forecasts future outcomes by analyzing data patterns, while agentic AI acts autonomously to achieve goals by combining predictive capabilities with autonomous planning, decision-making, and action-taking in an environment, often involving multiple agents working together with human guidance or oversight. The key difference is prediction (what might happen) versus autonomous action (making it happen).
A robust AML program that leverages advanced AI must also include strong governance to validate, monitor, and explain the outcomes of its AI systems. As AI becomes more integrated into compliance, regulators are shifting their focus from best practices to mandatory oversight and clear accountability to build trust and safety across the AI lifecycle.
This is a significant area of risk for many. Our survey found that while 59% of firms have a fully implemented AI assurance program, over 40% remain exposed to regulatory scrutiny. Frameworks like the UK’s AI Assurance Roadmap signal a clear trend: firms must be able to show their work for the technology that informs their compliance decisions, and “ensure it is developed and deployed responsibly”.

Unifying your AML defenses
There is a deliberate irony in providing a checklist for a domain that is rapidly outgrowing them. While the ten pillars above are essential for regulatory hygiene, the future of financial crime prevention lies in moving beyond a disjointed, mark-as-complete mindset.
As the FATF observed at the 2019 AI & Blockchain Summit, “stopping money laundering is not a box-ticking exercise… it’s about going after the money.” When compliance is viewed as a proactive mission rather than a technical obligation, it becomes a strategic shield rather than a regulatory burden.
To support this mission, our hyperscale platform, Mesh, integrates these essential pillars into one unified ecosystem:
- Proprietary risk intelligence: We ingest data directly from the source – sanctions lists, PEP registers, and global media – to ensure intelligence is as fresh as possible. This end-to-end data ownership means sanctions updates are searchable within hours, not days, ensuring your defense is always based on the latest global reality.
- Unified risk applications: Whether it is Customer Screening, Transaction Monitoring, or Payment Screening, our applications live on a single platform. This helps remove the silos that criminals exploit, providing a single, consistent view of risk across the entire customer lifecycle without stitching together multiple systems.
- Agentic AI for investigations: Moving beyond simple automation, agentic AI autonomously orchestrates the investigation process – from alert generation to SAR narrative drafting. These agents sit alongside human analysts in the workflow, presenting complete, evidence-backed case files that significantly enhance decision accuracy and speed.
Discover integrated AML compliance with Mesh
A cloud-based compliance platform, ComplyAdvantage Mesh combines industry-leading AML risk intelligence with actionable risk signals to screen customers and monitor their behavior in near real time.
Request a demoOriginally published 01 July 2020, updated 14 April 2026
Disclaimer: This is for general information only. The information presented does not constitute legal advice. ComplyAdvantage accepts no responsibility for any information contained herein and disclaims and excludes any liability in respect of the contents or for action taken based on this information.
Copyright © 2026 IVXS UK Limited (trading as ComplyAdvantage).
